Automattic steps in
Recently (late June 2023) a security vulnerability (CVE) in a widely used third party WordPress plug-in was discovered. Shortly after, the vendor released a working patched version of the software. By itself this wasn’t unusual, security patches for plug-ins are released all the time. But the way this update transpired was a little different and tells us a couple things that every business owner using WordPress should be aware of.
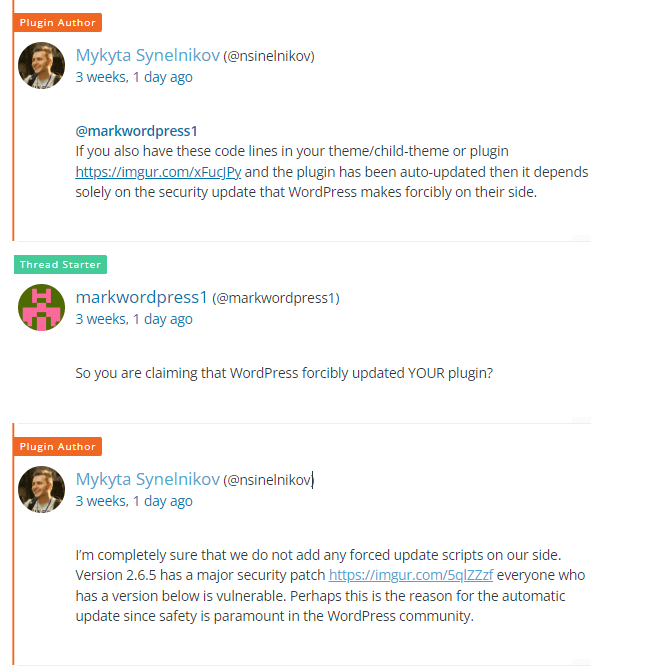
The short story is that Automattic, the parent company to WordPress pushed out a compulsory (read: forced) update for the plugin software. This action bypassed the normal process whereby WordPress site owners and hosts have control over when and how third-party software is updated.
The plug-in in question is Ultimate Member, the #1 WordPress plug-in for managing communities and online membership. First released in 2015, Ultimate Member (UM) is used by over 200,000 websites and has a thriving user community. From our experience, UM is generally regarded as the industry standard plug-in for adding membership functionality to your WordPress website.
WordPress site admins can be notified via various security plugins and hosting platforms when a plug-in has an update that fixes a security-related issue. And in those instances it is the site admin’s responsibility to update the plug-in either through a manual update or by enablingWordPress’ “auto-update” plugin setting. But the site admin is in control, which is important because plug-in updates can break things, and when and how they happen needs oversight. Though it is true that, in extreme cases, if a vulnerable plug-in is not updated and the issue is serious enough, a hosting provider may decide to disallow that plug-in or even shut down an entire site. However, even in those cases, the site admin would normally receive some kind of advanced notice.
In the case of this Ultimate Member update, Automattic took the unusual step of updating all installed Ultimate Member plug-ins using the WordPress core update service. That update resulted in lots of websites breaking or losing member community functions. We don’t know how many sites broke but it was likely hundreds if not thousands, given UM’s large install base.
Furthermore, the update that Automattic pushed out on July 1 didn’t actually fix the issue. It took three more days and two more versions to get the gap filled.
Now, to be clear, we aren’t disputing the importance of this update. From what we have surmised, this flaw was a big hairy one and needed to be addressed ASAP to keep WordPress sites and servers around the world from being compromised. But we were thrown off by how it happened and the fact that the forced update that was pushed to vulnerable sites didn’t succeed.
Key takeaways for all WordPress admins and site owners.
1. Compulsory updates can include updates to third party plug-ins
This may not be unprecedented but we’ve never experienced a forced update for a plug-in. Most likely this is only the case when a plug-in is really widely used and has a major security flaw but we don’t know for sure. We’re guessing Automattic has some kind of a formula for determining when they would need to force a third-party plug-in update, but so far there’s been no outbound communication from the vendor. So for now we just know it can happen.
2. You should be prepared to deactivate plug-ins
Even those that provide critical functionality on your website may need to be deactivated when a security event like this happens and there isn’t a fix available. Keeping an insecure vulnerable plug-in operating, leaves your business open to malicious actors and courts disaster. How you create this contingency plan is up to you. It could be as involved as setting up a second plug-in that provides redundant functionality or it could be as simple as preparing messaging that tells your site visitors that certain functionality is unavailable at the moment. The key is that you have that plan in place beforehand.
3. Don’t underestimate the value of keeping core plug-ins up-to-date
Doing this provides some level of resiliency because, if those core plug-ins are auto-updated as described above, the more up-to-date they are the less likely it is that things will break with an update. In other words, if you have a plug-in that is three or four updates behind, an emergent security update to that plug-in is more likely to break something on your site.
4. Use a website management resource
If your business has a critical web presence (as most do), you must have a reliable, responsive and informed resource managing that site. That person or that team can be in house or on call, part time or full time, onshore or offshore. The important thing is that they actively manage the site and are knowledgeable about its inner workings. Trying to onboard a developer or website manager in the midst of a security crisis is never a successful approach.
For more information and recommendations on website management, read our article Website Management Essentials: The six elements your business needs to create a successful website management program.
Our experience
For Tenrec, with this emergent Ultimate Member update, we had four clients whose websites were affected. For two of those clients, we had to disable the plug-in while we waited for Ultimate Member to release a patch that worked. This took three days (over a holiday weekend, of course). But in the end, the limitations caused by disabling the membership and community functions were far less disruptive than a security breach would have been.